SYN flooding attack detection by TCP handshake anomalies - Bellaïche - 2012 - Security and Communication Networks - Wiley Online Library
ddos - Is there any working solution against large SYN Flood request? - Information Security Stack Exchange

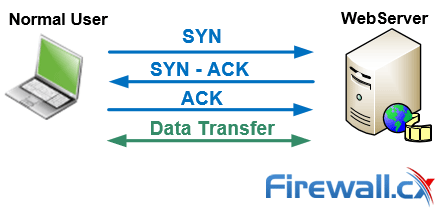







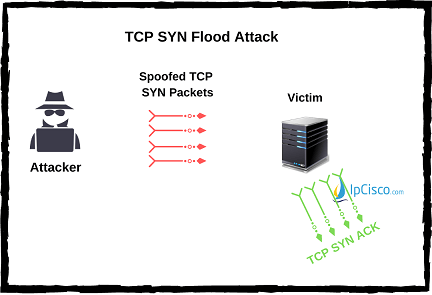

![IT430] Class 10: Denial of Service IT430] Class 10: Denial of Service](https://www.usna.edu/Users/cs/choi/it430/lec/l10/3way.png)